The Ol’ Invoice Scam
Employees of CSRA companies have to be more diligent than ever, before opening up emails that seem legitimate. In today’s P.U.T.T. video segment, our consultant, Patrick Reynolds got a call from a client about this very matter.
Employees of CSRA companies have to be more diligent than ever, before opening up emails that seem legitimate. In today’s P.U.T.T. video segment, our consultant, Patrick Reynolds got a call from a client about this very matter.

IT security is a measure of protection for a computer network and its data from any breach, leak, publication of private information, or attack. It’s the service that Crosslink Consulting provides. Patrick Reynolds has more in today’s P.U.T.T.

So, how has Patrick Reynolds made it 20 years in business? In this video, he explains his “why.”

Cross Link Consulting CEO, Patrick Reynolds had a few good reasons to cut the cake yesterday, next to Lookaway Hall in North Augusta and near Cross Link Consulting’s office building on Highway 25 in North Augusta. It’s the 20th Anniversary of his business and yesterday was also his 50th birthday! Reynolds told ABD at the party that he measures success by his ability to invest in and impact his 13 employees, like his Operations Manager, Jason Franklin (left of Reynolds). Cross Link Consulting had a slide show running on monitors

No road to business success is easy, but building and earning trust are key, especially in the cyber security field. Patrick Reynolds has more in today’s edition of P.U.T.T.

There are signs for you to know whether your data is separated out from other tenants in your building. Patrick Reynolds explains how your system should be set up in today’s edition of P.U.T.T.

Different companies and those employees may work in the same building. In today’s P.U.T.T. report, consultant, Patrick Reynolds explains how everyone can protect their data.

The simple answer is that one is annoying and the other can be dangerous to your business. Patrick Reynolds explains in today’s edition of P.U.T.T.
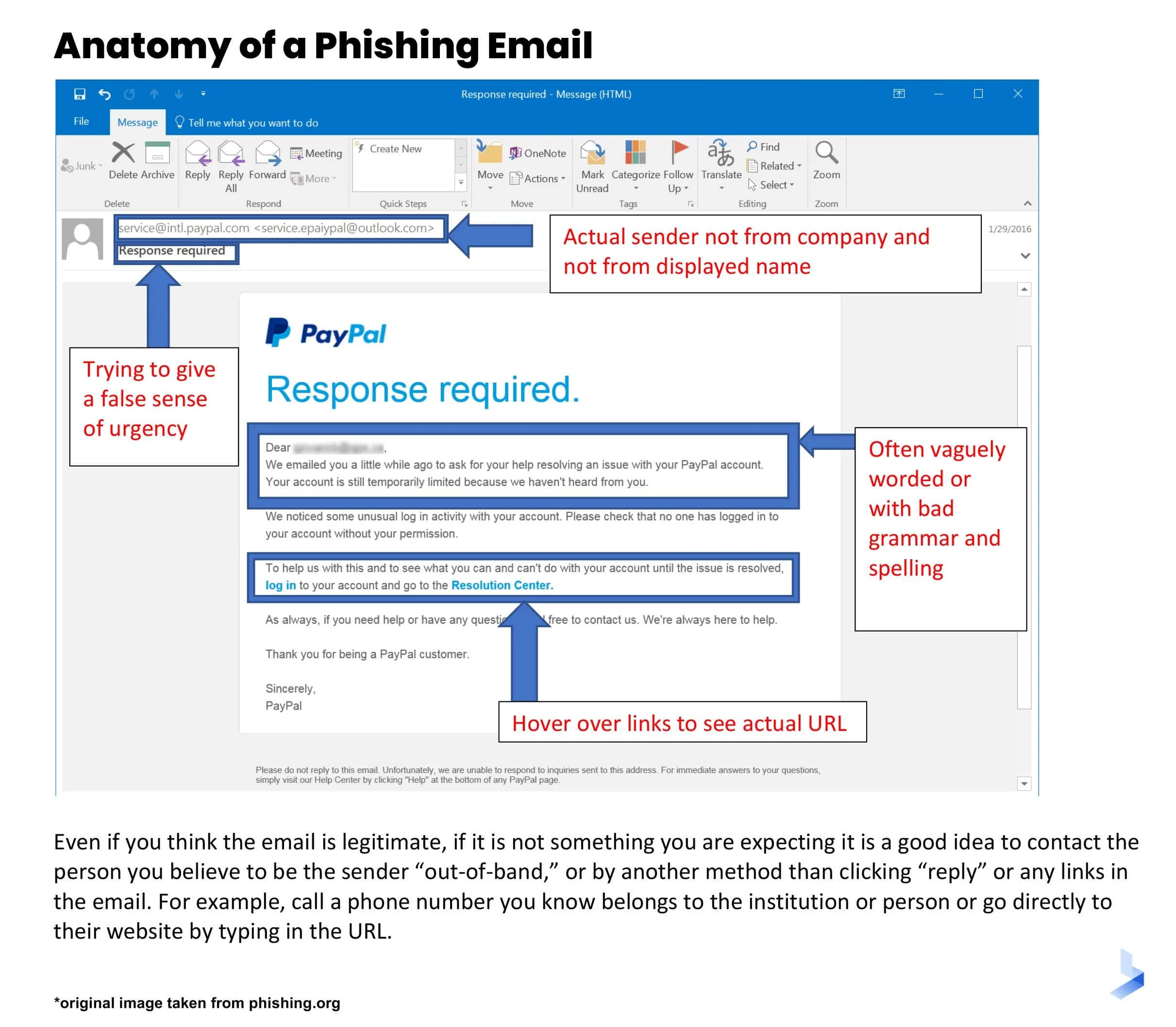
How do “bad actors” get to you through phishing? Let us count the ways. Emailing you with an invoice you don’t owe is one example. There are many others as Patrick Reynolds explains in today’s edition of P.U.T.T.
Phishing scams account for nearly 22 percent of all data breaches that occur, thus, securing it a position as one of the most prevalent cybercrimes. Nearly 83% of companies experienced phishing attacks. Patrick Reynolds has more in today’s edition of P.U.T.T.