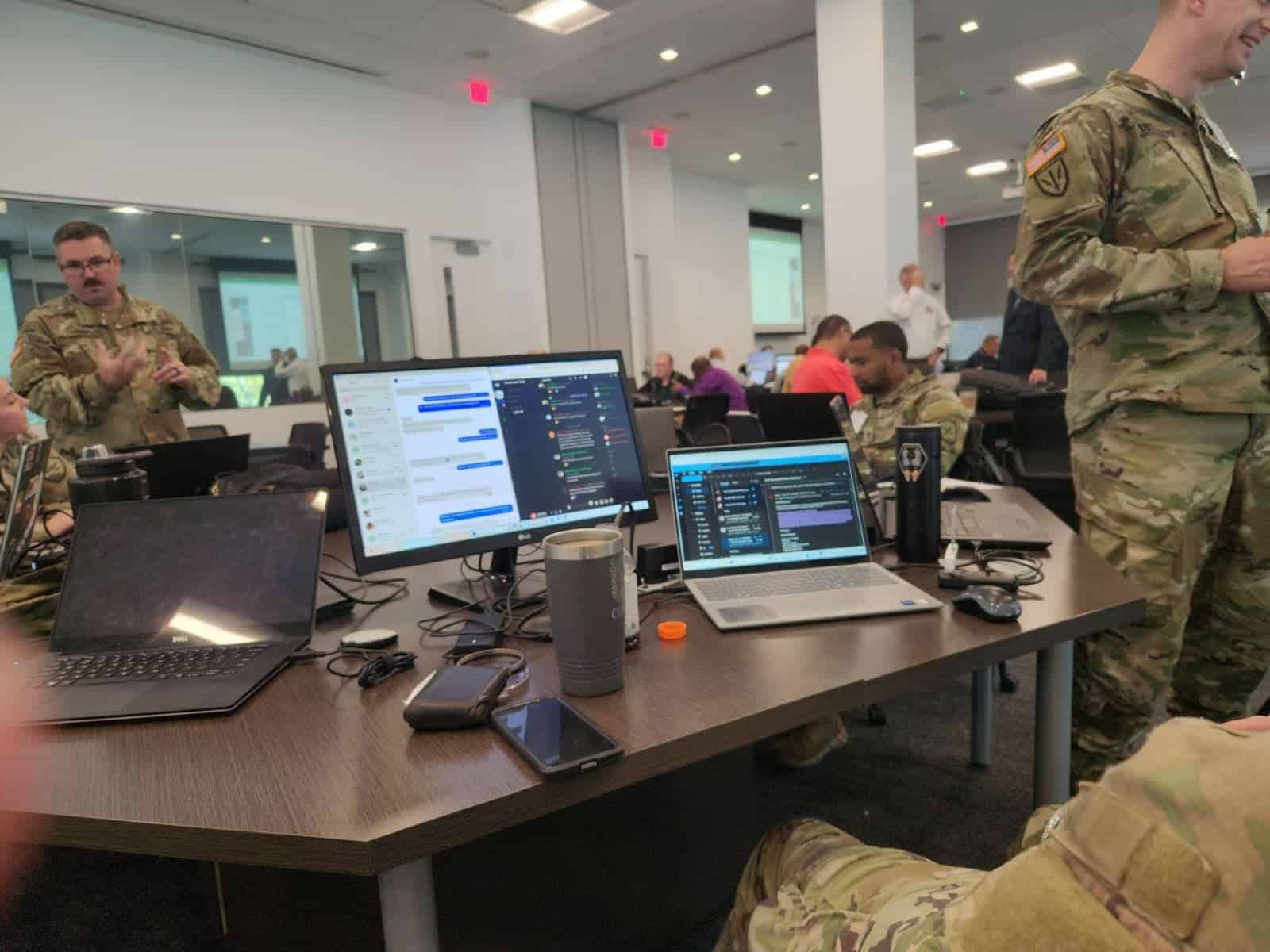
The men and women on the front line in the fight against hackers have spent the week in Augusta.
They have been participating in the Annual Cyber Dawg training exercise at the Georgia Cyber Innovation and Training Center. This is the fifth year the center has hosted the weeklong event.
Cyber Dawg brings together IT professionals from state agencies including the Georgia Lottery, Georgia Emergency Management Agency, and Georgia Public Safety Training Center.
The Georgia Army National Guard, a partner in Cyber Dawg, wages an attack on what is called the Cyber Range. It essentially creates a computer network in a bubble. It’s similar to gun ranges used for live fire weapons training.
“You have lots of different state entities coming together to practice defending an emulated network. It’s a real-world network, but it’s in our sandbox environment,” explained Johnathan Race, who helped build the Cyber Range. “They get to practice trying to defend against them, detect them, and perform all sorts of actions consequence-free, without ruining actual systems that they normally operate on a day-to-day basis.”
The Georgia Technology Authority’s Office of Information Security leads Cyber Dawg’s week of activities. It began in 2018 as Cyber Academy and transitioned to using the Cyber Range the following year.
“We have in the state kind of the situation where there’s a lot of transition, a lot of people transition in and out as private sector opportunities present themselves. People transition to better opportunities elsewhere,” said Mike Davies, deputy state Chief Information Security Officer (CISO). “So, we try to maintain a series of events and training, things such as Cyber Dawg that allow our information security professionals at the various agencies to get hands-on experience.”
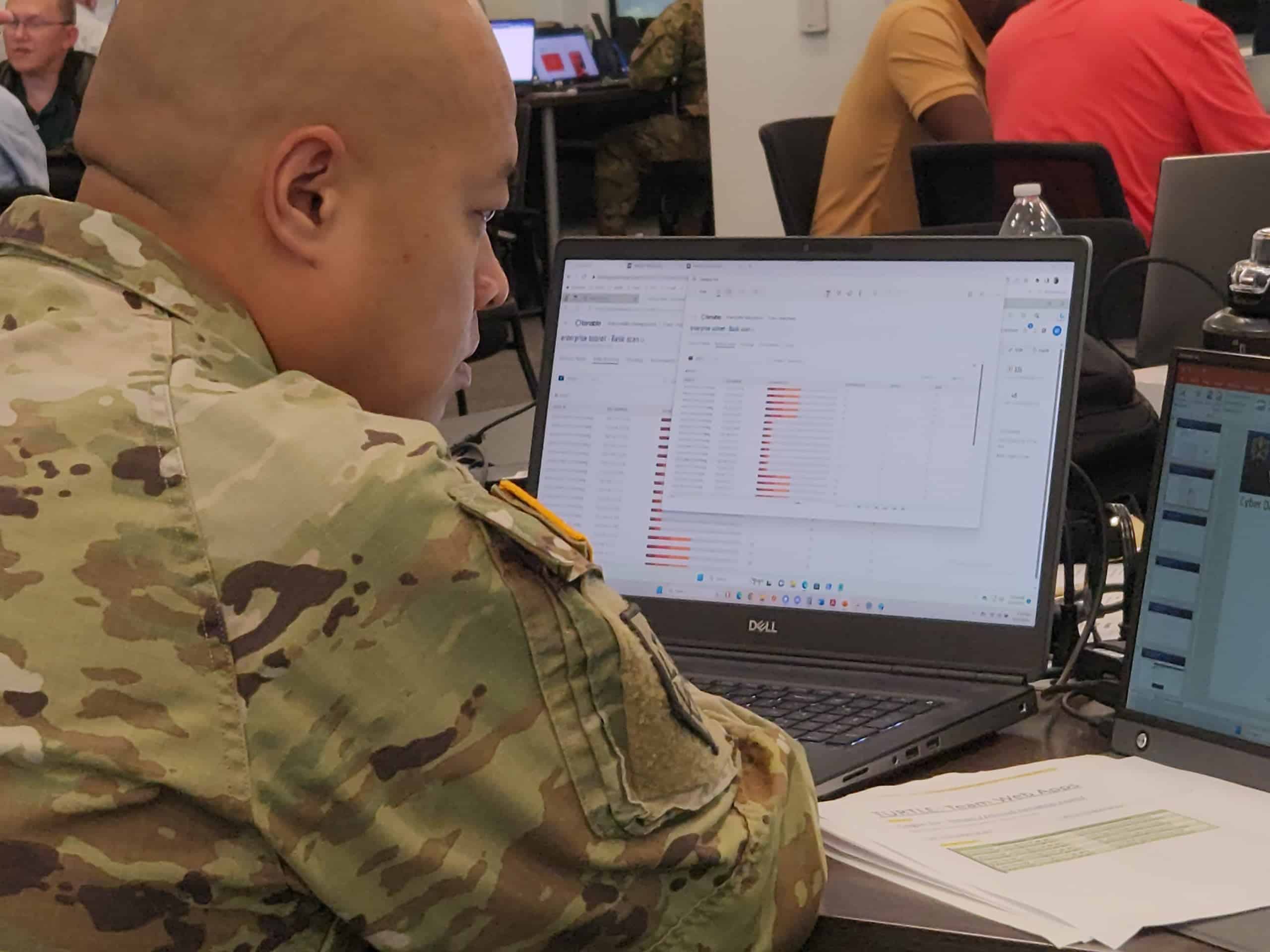
Davies said this is the first year they have been able to use the MITRE attack framework. MITRE Corporation, based in Massachusetts and Virginia, works with government, industry, and academia to protect networks from intrusions by hackers.
“The MITRE attack framework kind of allows the participants to begin to recognize different attack techniques and different attack patterns to then be able to do predictive analysis on where they should be looking next,” he said. “Certain threat actors follow a certain pattern, so they’ll use techniques to do initial infiltration or evidence gathering, which will follow by lateral movement. Culminating, of course, with the threat actor’s intent to do data infiltration or extortion.”
Davies said studying the patterns can help IT professionals predictively analyze where the threat attacker might be going next. It allows him to know what to look for.
 “We are all at certain risk, and if we don’t attend to our own cybersecurity, we put others at risk,” said Patrick Reynolds, president of Cross Link Consulting, a North Augusta-based IT and Cybersecurity firm. “Training exercises like Cyber Dawg are a great place for IT professionals to see how quickly they can be compromised, and how great the need is for continuous breach monitoring. The earlier a breach can be detected, the less damage our communities will suffer.”
“We are all at certain risk, and if we don’t attend to our own cybersecurity, we put others at risk,” said Patrick Reynolds, president of Cross Link Consulting, a North Augusta-based IT and Cybersecurity firm. “Training exercises like Cyber Dawg are a great place for IT professionals to see how quickly they can be compromised, and how great the need is for continuous breach monitoring. The earlier a breach can be detected, the less damage our communities will suffer.”
Race expects Cyber Dawg, or similar training exercises, will continue far into the future. He said such events keep IT professionals on the cutting edge of online security techniques.